

Fill out the form and an expert EC-Council Training Consultant will contact you to help you get all your questions answered.
The Certified Ethical Hacker (CEH) provides an in-depth understanding of ethical hacking phases, various attack vectors, and preventative countermeasures. It will teach you how hackers think and act so you will be better positioned to set up your security infrastructure and defend against attacks. By providing an understanding of system weaknesses and vulnerabilities, the CEH course helps students learn to protect their organizations and strengthen their security controls in order to minimize the risk of a malicious attack.
CEH was built to incorporate a hands-on environment and systematic process across each ethical hacking domain and methodology, giving you the opportunity to work toward proving the required knowledge and skills needed to achieve the CEH credential and perform the job of an ethical hacker.
Now in its 12th version, CEH continues to evolve with the latest operating systems, tools, tactics, exploits, and technologies.
About the Certified Ethical Hacker (CEH) Course

(Windows 11, Windows Servers, Linux, Ubuntu, Android)

CEH Knowledge Exam
CEH Practical Exam


CEH is divided into 20 modules and delivered through a carefully curated training plan that typically spans across 5 days. As you progress through your training, each module offers extensive hands-on lab components that allow you to practice the techniques and procedures taught in the program in real-time on live machines.
Ethical Hacking Labs
With over 200 hands-on labs, conducted in our cyber range environment, you will have the opportunity to practice every learning objective in the course on live machines and vulnerable targets. Pre-loaded with over 3,500 hacking tools and a variety of operating systems, you will gain unprecedented exposure to and hands-on experience with the most common security tools, latest vulnerabilities, and widely used operating systems on the market. Our range is web accessible, allowing you to study and practice from anywhere with a connection.
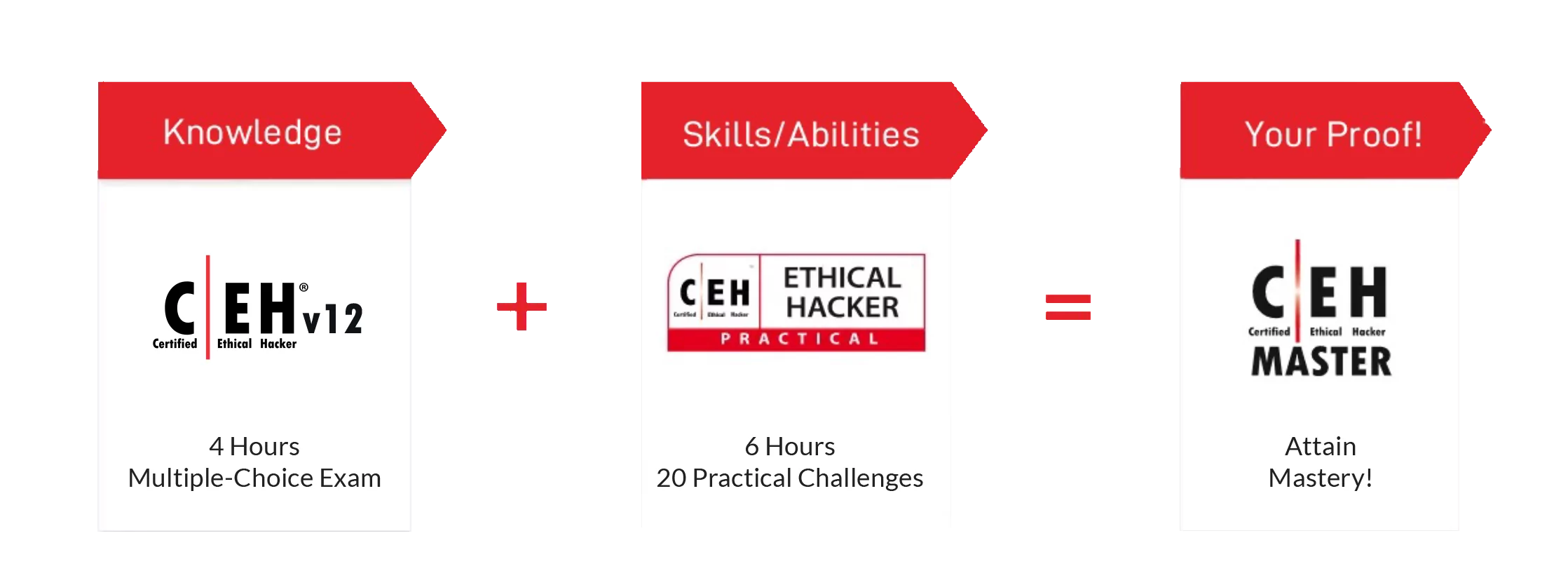
The CEH exam is a 4-hour exam with 125 multiple-choice questions. This knowledge-based exam will test your skills in Information Security Threats and Attack Vectors, Attack Detection, Attack Prevention, Procedures, Methodologies and more!
CEH Practical CertificationCEH Practical is a 6-hour, rigorous exam that requires you to demonstrate the skills and abilities of ethical hacking techniques such as:
This is the next step to becoming a CEH Master after you have achieved your CEH certification. Within CEH Practical, you have a limited amount of time to complete 20 challenges that test your skills and proficiency in a performance-based cyber range. This exam is NOT a simulation and incorporates a live corporate network of VMs and applications with solutions to uncover vulnerabilities.
CEH MasterUpon Completing the CEH (Master) program, which consists of CEH and CEH (Practical), the CEH (Master) designation is awarded. C|EH Masters have shown proficiency at a master level in the knowledge, skills, and abilities of ethical hacking with a total 6 hours of testing to prove their competency. Top top 10 performers in both CEH and CEH Practical exams are showcased on the CEH Master Global Ethical Hacking Leaderboard.
CEH Exam at a Glance| Exam Details | CEH (MCQ Exam) | CEH (Practical) |
|---|---|---|
| Number of Questions/Practical Challenges | 125 | 20 |
| Test Duration | 4 Hours | 6 Hours |
| Test Format | Multiple Choice Questions | iLabs Cyber Range |
| Test Delivery | ECC Exam, VUE | |
| Availability | - | Aspen - iLabs |
| Exam Prefix | 312-50 (ECC Exam), 312-50 (VUE) | |
| Passing Score | Please refer to (https://cert.eccouncil.org/faq.html) | 70% |
The CEH v12 program helps you develop real-world experience in ethical hacking through the hands-on CEH practice environment. CEH Engage equips you with the skills to prove that you have what it takes to be a great ethical hacker.
Your security assessment objectives will be presented as a series of flags (questions you must answer in the Cyber Range by performing ethical hacking activities on the target organization).
New to CEH v12, students will embark on their first emulated ethical hacking engagement. This 4-phase engagement requires students to think critically and test the knowledge and skills gained by capturing a series of flags in each phase, demonstrating the live application of skills and abilities in a consequence-free environment through EC-Council’s new Cyber Range.
As you complete your training and hands-on labs, CEH Engage lets you apply everything you have learned in a mock ethical hacking engagement. This 4-part security engagement gives you a real ethical hacking engagement experience from start to finish against an emulated organization. Using our capture-the-flag-style range, you will complete your engagement by answering “flag” questions as you progress.
The C|EH Global Challenges occur every month, providing capture-the-flag style competitions that expose students to various new technologies and platforms, from web applications, OT, IoT, SCADA, and ICS systems to cloud and hybrid environments. Our Compete structure lets ethical hackers fight their way to the top of the leaderboard each month in these 4-hour curated CTFs. Objective-based flags are designed around the ethical hacking process, keeping skills current, testing critical thinking abilities, and covering the latest vulnerabilities and exploits as they are discovered. Hosted 100% online in EC-Council’s Cyber Range, candidates race the clock in scenario-based engagements against fully developed network and application environments with real operating systems, real networks, tools, and vulnerabilities to practice, engage, compete, build, and hone their cyber skills against various new target organizations.
| Month | Skill Challenge |
|---|---|
| October 2022 | OWASP Top 10 Web Application Threat Vectors |
| November 2022 | Ransomware/Malware Analysis |
| January 2023 | System Hacking and Privilege Escalation |
| February 2023 | Web Application Hacking and Pen Testing |
| March 2023 | Cloud Attack/Hacking |
| April 2023 | Social Engineering/Phishing attacks |
| May 2023 | IoT Attack/Hacking |
| June 2023 | Wi-Fi Network Attack/Hacking |
| July 2023 | DOS/DDoS Attack |
| August 2023 | Mobile Attack/Hacking |
| September 2023 | Supply Chain Cyber Attacks |
20 Modules that help you master the foundations of
Ethical Hacking and prepare to challenge the CEH certification exam.
Cover the fundamentals of key issues in the information security world, including the basics of ethical hacking, information security controls, relevant laws, and standard procedures.
Elements of Information Security, Cyber Kill Chain Methodology, MITRE ATT&CK Framework, Hacker Classes, Ethical Hacking, Information Assurance (IA), Risk Management, Incident Management, PCI DSS, HIPPA, SOX, GDPR
Learn how to use the latest techniques and tools to perform foot printing and reconnaissance, a critical pre-attack phase of the ethical hacking process.
Over 30 hands-on exercises with real-life simulated targets to build skills on how to:
Footprinting, Advanced Google Hacking Techniques, Deep and Dark Web Footprinting, Competitive Intelligence Gathering, Website Footprinting, Website Mirroring, Email Footprinting, Whois Lookup, DNS Footprinting, Traceroute Analysis, Footprinting Tools
Cover the fundamentals of key issues in the information security world, including the basics of ethical hacking, information security controls, relevant laws, and standard procedures.
Over 10 hands-on exercises with real-life simulated targets to build skills on how to:
Network Scanning, Host Discovery Techniques, Port Scanning Techniques, Service Version Discovery, OS Discovery, Banner Grabbing, OS Fingerprinting, Packet Fragmentation, Source Routing, IP Address Spoofing, Scanning Tools
Learn various enumeration techniques, such as Border Gateway Protocol (BGP) and Network File Sharing (NFS) exploits, and associated countermeasures
Over 20 hands-on exercises with real-life simulated targets to build skills on how to:
Enumeration, NetBIOS Enumeration, SNMP Enumeration, LDAP Enumeration, NTP Enumeration, NFS Enumeration, SMTP Enumeration, DNS Cache Snooping, DNSSEC Zone Walking, IPsec Enumeration, VoIP Enumeration, RPC Enumeration, Unix/Linux User Enumeration, Enumeration Tools
Learn various enumeration techniques, such as Border Gateway Protocol (BGP) and Network File Sharing (NFS) exploits, and associated countermeasures
Over 20 hands-on exercises with real-life simulated targets to build skills on how to:
Enumeration, NetBIOS Enumeration, SNMP Enumeration, LDAP Enumeration, NTP Enumeration, NFS Enumeration, SMTP Enumeration, DNS Cache Snooping, DNSSEC Zone Walking, IPsec Enumeration, VoIP Enumeration, RPC Enumeration, Unix/Linux User Enumeration, Enumeration Tools
Learn about the various system hacking methodologies—including steganography, steganalysis attacks, and covering tracks—used to discover system and network vulnerabilities.
Over 25 hands-on exercises with real-life simulated targets to build skills on how to:
Password Cracking, Password Attacks, Wire Sniffing, Password-Cracking Tools, Vulnerability Exploitation, Buffer Overflow, Privilege Escalation, Privilege Escalation Tools, Keylogger, Spyware, Anti-Keyloggers, Anti-Spyware, Rootkits, Anti-Rootkits, Steganography, Steganography Tools, Steganalysis, Steganography Detection Tools, Maintaining Persistence, Post Exploitation, Clearing Logs, Covering Tracks, Track-Covering Tools
Get an introduction to the different types of malware, such as Trojans, viruses, and worms, as well as system auditing for malware attacks, malware analysis, and countermeasures.
Over 20 hands-on exercises with real-life simulated targets to build skills on how to:
Malware, Components of Malware, APT, Trojan, Types of Trojans, Exploit Kits, Virus, Virus Lifecycle, Types of Viruses, Ransomware, Computer Worms, Fileless Malware, Malware Analysis, Static Malware Analysis, Dynamic Malware Analysis, Virus Detection Methods, Trojan Analysis, Virus Analysis, Fileless Malware Analysis, Anti-Trojan Software, Antivirus Software, Fileless Malware Detection Tools
Learn about packet-sniffing techniques and how to use them to discover network vulnerabilities, as well as countermeasures to defend against sniffing attacks
Over 10 hands-on exercises with real-life simulated targets to build skills on how to:
Network Sniffing, Wiretapping, MAC Flooding, DHCP Starvation Attack, ARP Spoofing Attack, ARP Poisoning, ARP Poisoning Tools, MAC Spoofing, STP Attack, DNS Poisoning, DNS Poisoning Tools, Sniffing Tools, Sniffer Detection Techniques, Promiscuous Detection Tools
Learn social engineering concepts and techniques, including how to identify theft attempts, audit human-level vulnerabilities, and suggest social engineering countermeasures.
Over 4 hands-on exercises with real-life simulated targets to build skills on how to:
Social Engineering, Types of Social Engineering, Phishing, Phishing Tools, Insider Threats/Insider Attacks, Identity Theft
Learn about different Denial of Service (DoS) and Distributed DoS (DDoS) attack techniques, as well as the tools used to audit a target and devise DoS and DDoS countermeasures and protections.
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
DoS Attack, DDoS Attack, Botnets, DoS/DDoS Attack Techniques, DoS/DDoS Attack Tools, DoS/DDoS Attack Detection Techniques, DoS/DDoS Protection Tools
Understand the various session hijacking techniques used to discover network-level session management, authentication, authorization, and cryptographic weaknesses and associated countermeasures.
Over 4 hands-on exercises with real-life simulated targets to build skills on how to:
Session Hijacking, Types of Session Hijacking, Spoofing, Application-Level Session Hijacking, Man-in-the-Browser Attack, Client-side Attacks, Session Replay Attacks, Session Fixation Attack, CRIME Attack, Network Level Session Hijacking, TCP/IP Hijacking, Session Hijacking Tools, Session Hijacking Detection Methods, Session Hijacking Prevention Tools
Get introduced to firewall, intrusion detection system, and honeypot evasion techniques; the tools used to audit a network perimeter for weaknesses; and countermeasures.
Over 7 hands-on exercises with real-life simulated targets to build skills on how to:
Intrusion Detection System (IDS), Intrusion Prevention System (IPS), Firewall, Types of Firewalls, Honeypot, Intrusion Detection Tools, Intrusion Prevention Tools, IDS Evasion Techniques, Firewall Evasion Techniques, Evading NAC and Endpoint Security, IDS/Firewall Evading Tools, Honeypot Detection Tools
Learn about web server attacks, including a comprehensive attack methodology used to audit vulnerabilities in web server infrastructures and countermeasures.
Over 8 hands-on exercises with real-life simulated targets to build skills on how to:
Web Server Operations, Web Server Attacks, DNS Server Hijacking, Website Defacement, Web Cache Poisoning Attack, Web Server Attack Methodology, Web Server Attack Tools, Web Server Security Tools, Patch Management, Patch Management Tools
Learn about web application attacks, including a comprehensive web application hacking methodology used to audit vulnerabilities in web applications and countermeasures.
Over 15 hands-on exercises with real-life simulated targets to build skills on how to:
Web Application Architecture, Web Application Threats, OWASP Top 10 Application Security Risks – 2021, Web Application Hacking Methodology, Web API, Webhooks, and Web Shell, Web API Hacking Methodology, Web Application Security
Learn about SQL injection attack techniques, injection detection tools, and countermeasures to detect and defend against SQL injection attempts.
Over 4 hands-on exercises with real-life simulated targets to build skills on how to:
SQL Injection, Types of SQL injection, Blind SQL Injection, SQL Injection Methodology, SQL Injection Tools, Signature Evasion Techniques, SQL Injection Detection Tools
Learn about wireless encryption, wireless hacking methodologies and tools, and Wi-Fi security tools.
Over 3 hands-on exercises with real-life simulated targets to build skills on how to:
Wireless Terminology, Wireless Networks, Wireless Encryption, Wireless Threats, Wireless Hacking Methodology, Wi-Fi Encryption Cracking, WEP/WPA/WPA2 Cracking Tools, Bluetooth Hacking, Bluetooth Threats, Wi-Fi Security Auditing Tools, Bluetooth Security Tools
Learn about mobile platform attack vectors, Android vulnerability exploits, and mobile security guidelines and tools.
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
Mobile Platform Attack Vectors, OWASP Top 10 Mobile Risks, App Sandboxing, SMS Phishing Attack (SMiShing), Android Rooting, Hacking Android Devices, Android Security Tools, Jailbreaking iOS, Hacking iOS Devices, iOS Device Security Tools, Mobile Device Management (MDM), OWASP Top 10 Mobile Controls, Mobile Security Tools
Learn about packet-sniffing techniques and how to use them to discover network vulnerabilities, as well as countermeasures to defend against sniffing attacks
Over 2 hands-on exercises with real-life simulated targets to build skills on how to:
IoT Architecture, IoT Communication Models, OWASP Top 10 IoT Threats, IoT Vulnerabilities, IoT Hacking Methodology, IoT Hacking Tools, IoT Security Tools, IT/OT Convergence (IIOT), ICS/SCADA, OT Vulnerabilities, OT Attacks, OT Hacking Methodology, OT Hacking Tools, OT Security Tools
Learn different cloud computing concepts, such as container technologies and server less computing, various cloud-based threats and attacks, and cloud security techniques and tools.
Over 5 hands-on exercises with real-life simulated targets to build skills on how to:
Cloud Computing, Types of Cloud Computing Services, Cloud Deployment Models, Fog and Edge Computing, Cloud Service Providers, Container, Docker, Kubernetes, Serverless Computing, OWASP Top 10 Cloud Security Risks, Container and Kubernetes Vulnerabilities, Cloud Attacks, Cloud Hacking, Cloud Network Security, Cloud Security Controls, Cloud Security Tools
In the final module, learn about cryptography and ciphers, public-key infrastructure, cryptography attacks, and cryptanalysis tools.
Over 10 hands-on exercises with real-life simulated targets to build skills on how to:
Cryptography, Encryption Algorithms, MD5 and MD6 Hash Calculators, Cryptography Tools, Public Key Infrastructure (PKI), Email Encryption, Disk Encryption, Cryptanalysis, Cryptography Attacks, Key Stretching
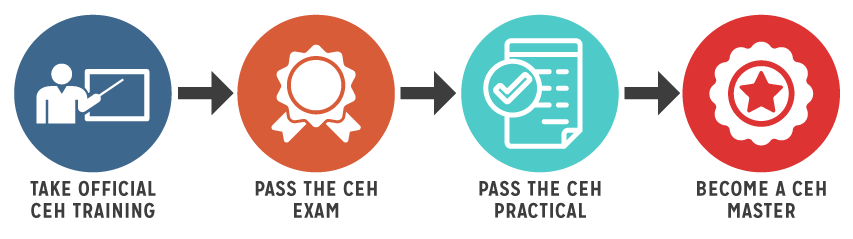
After taking an authorized course, candidates can attempt the CEH exam. Candidates that successfully pass the exam will receive their CEH certificate and membership privileges. After proving knowledge by achieving the CEH credential, candidates have the added option to proceed to attempt the CEH (Practical) exam to prove their skills and abilities. The CEH (Practical) is a 6-hour practical exam created by subject matter experts in the ethical hacking industry. The exam tests skills and abilities in a timed environment across major operating systems, databases, and networks. Candidates with both the CEH and CEH (Practical) certifications are designated as CEH Masters, having validated the full scope of their abilities.
Exam Title: Certified Ethical Hacker (ANSI)
Exam Code: 312-50 (ECC EXAM), 312-50 (VUE)
Number of Questions: 125
Test Format: Multiple Choice
Duration: 4 Hours
Availability: ECC EXAM* / VUE
CEH Certification Exam earned College Credit Recommendations from the American Council on Education (ACE) For more info, click here.
To earn the CEH Master certification, you must pass the CEH Practical exam. The CEH Practical Exam was designed to give students a chance to prove they can execute the principals taught in the CEH course. The practical exam requires you to demonstrate the application of ethical hacking techniques such as threat vector identification, network scanning, OS detection, vulnerability analysis, system hacking, and more.
The CEH Practical does not contain simulations. Rather, you will be challenging a live range which was designed to mimic a corporate network through the use of live virtual machines, networks, and applications.
Successfully navigating and completing the challenges found in the CEH (Practical) Exam is the next step after attaining the Certified Ethical Hacker (CEH) certification. Successfully passing both the CEH exam and the CEH Practical will earn you the additional certification of CEH Master.
While we strongly recommend that candidates take the CEH and pass the CEH exam, there are no predefined eligibility criteria for those interested in attempting the CEH (Practical) exam.
We know that traveling to an exam center can be difficult for many. We are pleased to announce that you can take the CEH (Practical) exam from the comfort of your home, but you need to be prepared to be proctored by a dedicated EC-Council Proctor certification team under strict supervision.
The exam dashboard code is valid for 3 months from the date of receipt. Should you require the exam dashboard code validity to be extended, kindly contact [email protected] before the expiry date. Only valid/ active codes can be extended. The exam needs to be scheduled a min 3 days prior to the desired exam date. Exam slots are subject to availability.
The trust that the industry places in our credentials is very important to us. We see it as our duty to ensure that the holders of this credential are proven hands-on, ethical hackers who are able to perform in the real world to solve real-world challenges. As such, the CEH (Master) is designed as a hands-on exam that will test the skills of the ethical hacker BEYOND just their knowledge. This exam is a proctored, practical exam that can last up to 6 hours.
We know that traveling to an exam center can be difficult for many. We are pleased to announce that you can take the CEH (Practical) exam from the comfort of your home, but you need to be prepared to be proctored by a dedicated EC-Council Proctor certification team under strict supervision.
Training for either the Certified Penetration Testing Professional (CPENT) course or the Computer Hacking Forensic Investigator (CHFI) course will be given to each student via EC-Council’s online, self-paced, streaming video program. Whether you want to add pen-test skills or computer forensic skills to your program, MasterClass has you covered.
Teaches students how to apply the concepts and tools taught in the CEH program to a pen-test methodology in a live cyber range.
CHFI (Computer Forensics):
Teaches students a methodological approach to computer forensics including searching and seizing, chain-of-custody, acquisition, preservation, analysis and reporting of digital evidence.
The MasterClass Certified Ethical Hacker program includes two courses and two certifications:
Students will attend the live Certified Ethical Hacker (CEH) Course which will teach students the 5 phases of Ethical Hacking and show them how to use the tools the hackers use in each of the phases. The course will prepare students for the CEH certification exam as well as the CEH Practical exam. Successful candidates who pass both will earn the CEH Master credential.
In addition to the two multiple choice certification exams, students will also be given the CEH practical exam. This exam is conducted on a live cyber range with up to 12 hours allotted to complete it. Students who opt to take the pen-test track (CPENT) will also be given the CPENT practical exam. This exam is conducted on a live cyber range with up to 12 hours allotted to complete it. These exams will allow candidates to prove that not only can they pass a test, but they can apply their knowledge in a real-world scenario.
As an iClass Club member, you receive unlimited access to EC-Council’s library of video courses. Upgrade to live classes for only $499 each during the subscription year.
You can even finance your Club membership through our partnership with Affirm. In the cart, you’ll be able to split your purchase into easy monthly payments. Term lengths range from 3 to 36 months depending on eligibility and purchase amount, with rates starting as low as 0% APR.
*Your rate will be 0% APR or 10–30% APR based on credit and is subject to an eligibility check. 0% APR is subject to change. Payment options through Affirm are provided by these lending partners: affirm.com/lenders. Options depend on your purchase amount, and a down payment may be required. US Residents Only.
Certification Club Benefits:
Don’t limit yourself to one class per year, join the iClass Club and get your cybersecurity training directly from the source! No one course can make you an expert, so take advantage of EC-Council Master trainers in each subject area and become a well-rounded cybersecurity professional.
For approximately the cost of one live course, the iClass Club will stretch your budget from one course to many. With savings like that, you can afford to build a strong foundation of cybersecurity knowledge in ethical hacking, pen testing, network defense, incident response, computer forensics, and so much more!
One Year Subscription
Access to EC-Council’s full library of on-demand courses
Move to “enhance” to upgrade your experience.
During your subscription, you can upgrade to a live course for $499!
Official Printed Courseware
Lastly, receive ongoing professional development by moving to the Continuing Education phase!
One year of CodeRed
Continue to learn and gather continuing education credits with CODERED!
Premium Content: 4000+ Premium Videos
Fresh Content: New courses and content are added weekly to keep up with the latest skills and technologies.
CodeRed course videos come with lab demos to reinforce course learning concepts and create a constant career learning companion.
Ready to sign up for the club subscription?
Certification Club Terms:
*Not all courses and workshops have associated Labs and exams. Club members must complete 100% of a course before requesting their next course and to be eligible for that course’s exam voucher. CCISO students must meet the eligibility requirements to challenge the CCISO exam. Students who do not meet the CCISO qualifications must take the EISM exam. CodeRed subscription 12 months. Club membership applicable to EC-Council classes only and does not apply to third party or Hacker Halted classes. Devices such as drones or STORMs must be purchased separately at regular price. Drones and STORMs only ship to the US. Students outside of the US can attend drone workshops but must obtain a drone on their own. If a course version changes while your program is still active, you will be given updated material. If a course version changes after your Club is expired, you will need to purchase an extension to get the new version. Club valid for one year and term begins 24 hours after payment is received. After a period of one (1) year the program expires, and all courses are turned off. Lab access term is for 6 months from when a course is assigned. Additional lab time can be added for no extra charge upon request. Labs will not be extended beyond the Club term. Speak to your rep to extend your Club term for 1 year. Renewal price for the Club is $999. Discount not stackable. The Club is a single user license meaning that the courses cannot be shared, and the club is non-transferable.